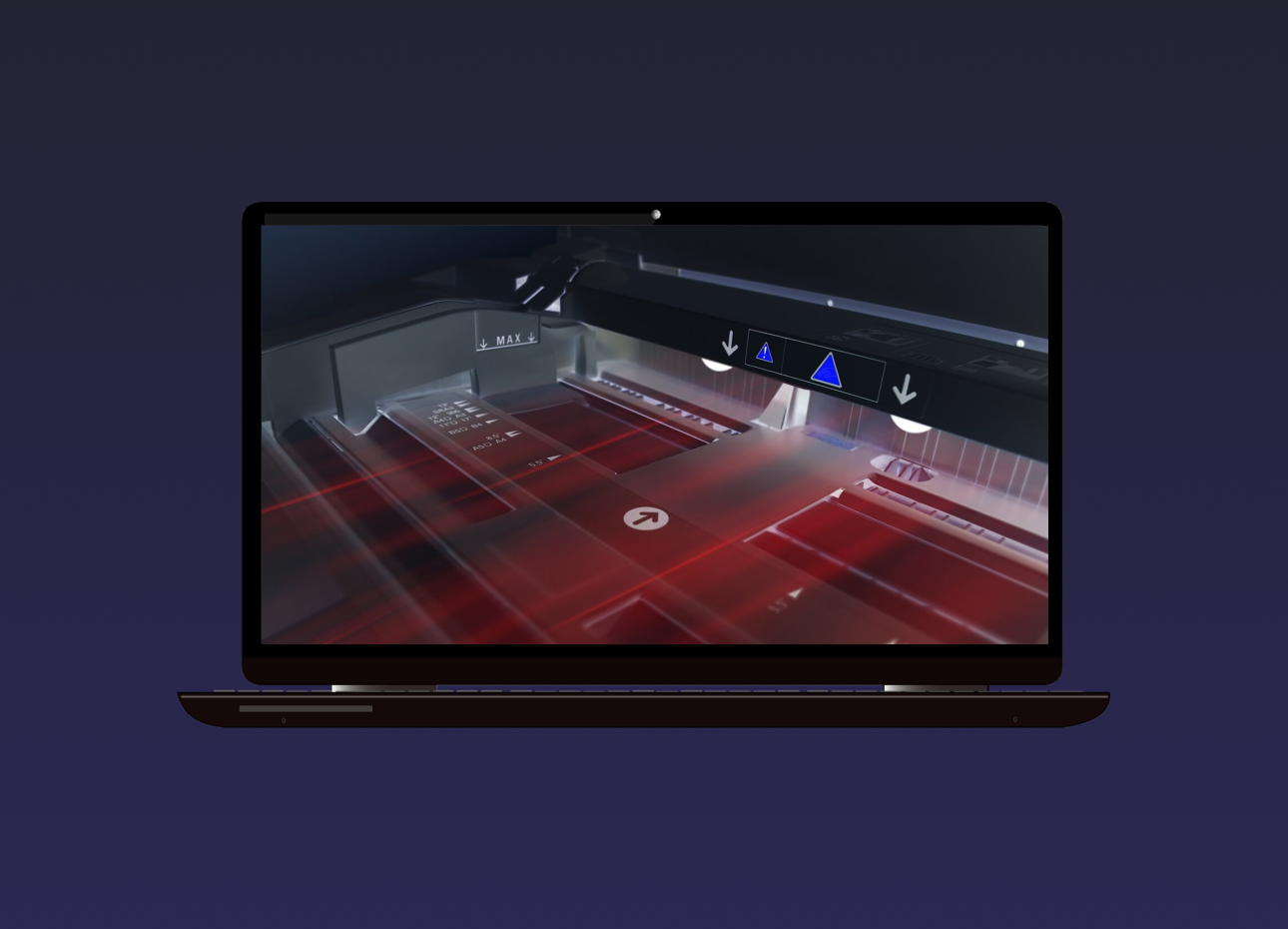
Trucell Announced as Preferred Reseller of LG Diagnostic Displays in Australia
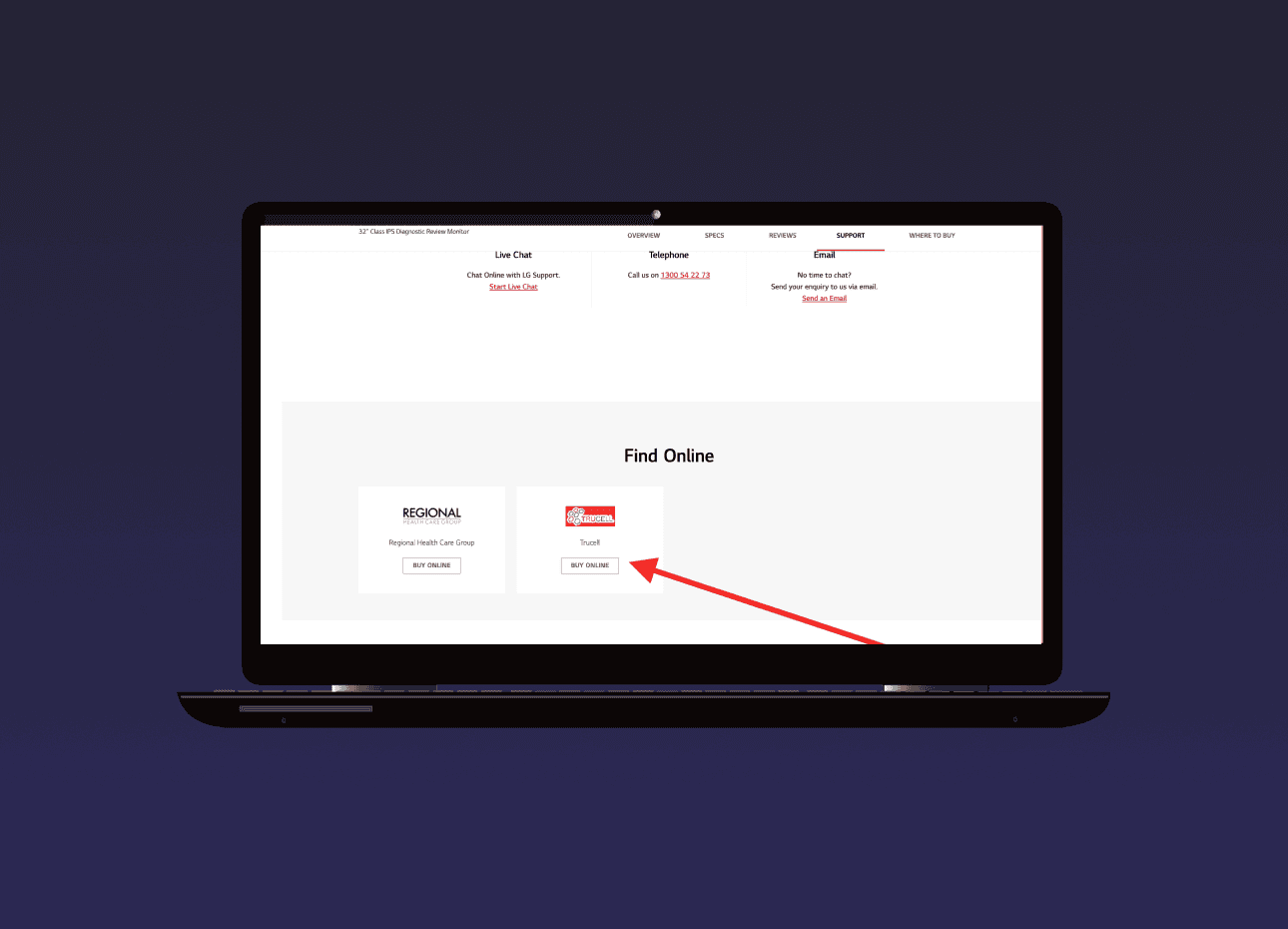
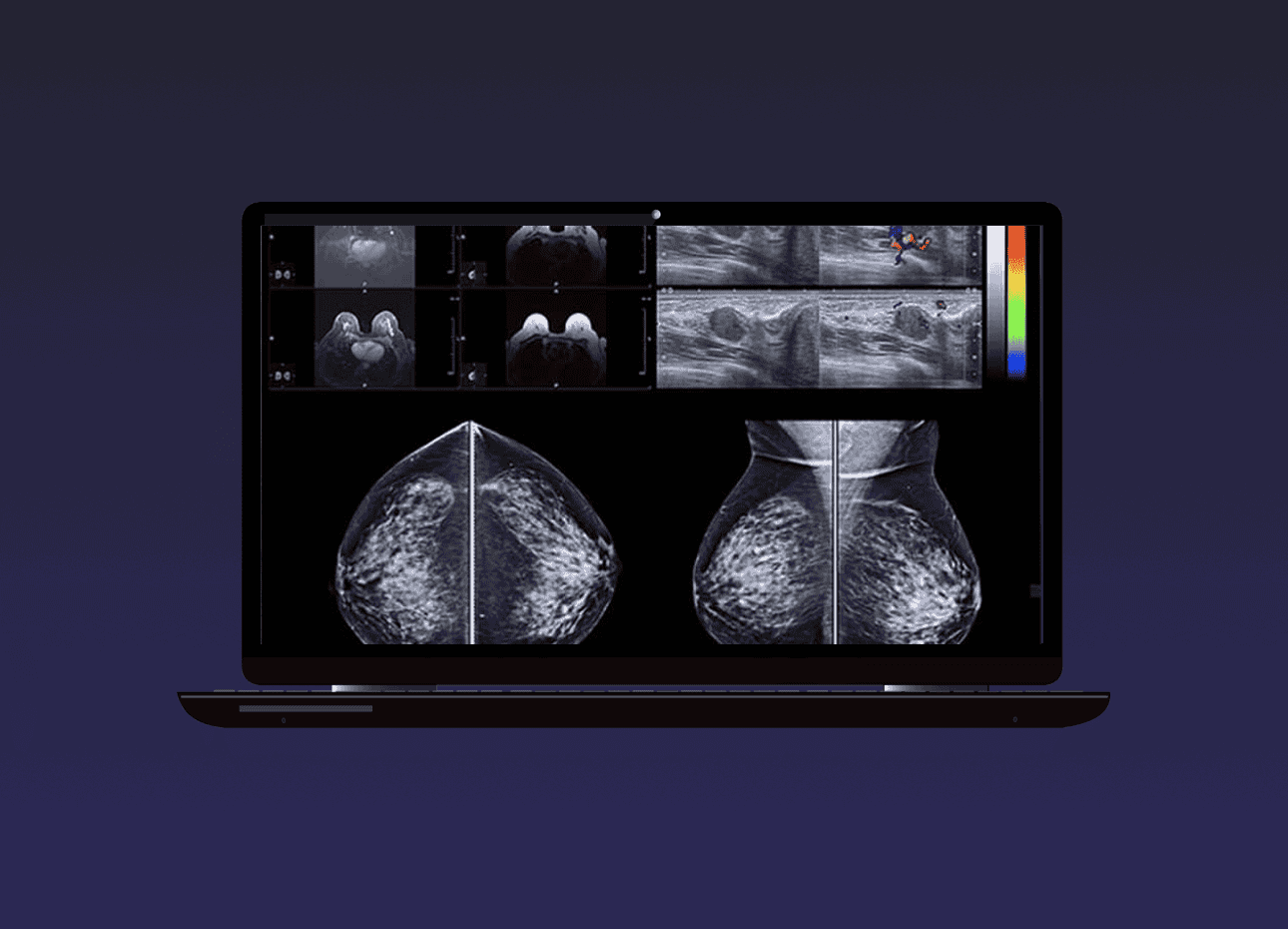
Trucell Pty Ltd, a leading provider of medical imaging solutions in Australia, is proud to announce that it has been selected by LG Electronics as one of its two preferred resellers for LG Diagnostic Displays in Australia. This partnership shows Trucell’s commitment to providing the highest quality medical imaging technology to health care providers across the country. LG Electronics, a global leader in hardware and technology, has recognised Trucell’s commitment to greatness and customer service in the medical imaging sector. This partnership will allow Trucell to offer LG’s state of the art diagnostic displays, known for their exceptional clarity, accuracy, and reliability, to a wider range of health care providers. LG Diagnostic Displays are designed to meet the demand of today’s health care industry. They offer superior image quality, making sure accurate diagnoses and patient treatment. With this partnership, Trucell will be able to provide these superior displays to hospitals,…